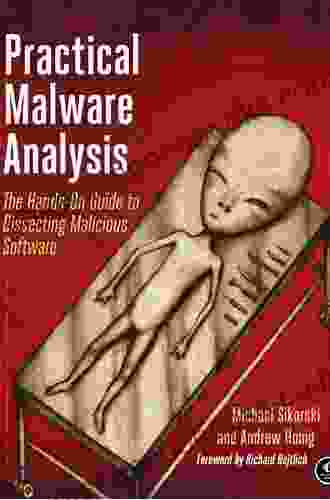
Unveiling the Secrets: A Comprehensive Guide to Dissecting Malicious Software

4.8 out of 5
| Language | : | English |
| File size | : | 11518 KB |
| Text-to-Speech | : | Enabled |
| Screen Reader | : | Supported |
| Print length | : | 802 pages |
Empower Yourself with the 'Hands-On Guide to Dissecting Malicious Software'
In the realm of cybersecurity, the battle against malicious software (malware) rages on. As cyber threats evolve and become more sophisticated, it's paramount to equip ourselves with the knowledge and skills to decipher and neutralize these digital adversaries.
Introducing the 'Hands-On Guide to Dissecting Malicious Software,' a comprehensive resource that empowers you to embark on a journey of reverse engineering, analysis, and mitigation techniques. This meticulously crafted guide is your gateway to understanding the inner workings of malware, enabling you to effectively combat cyber threats and protect your digital assets.
Delve into the Anatomy of Malware
This guide takes you on a meticulous exploration of the anatomy of malware, delving into the various types of malicious software, their modes of operation, and their impact on systems and networks.
- Uncover the techniques used by malware to infect and spread, including social engineering, phishing, and drive-by downloads.
- Understand the different types of malware, such as viruses, worms, trojans, and ransomware, and their unique characteristics.
- Gain insights into the methods malware employs to exploit vulnerabilities, compromise systems, and steal sensitive information.
Master Reverse Engineering Techniques
The 'Hands-On Guide to Dissecting Malicious Software' equips you with a comprehensive toolkit of reverse engineering techniques, empowering you to delve into the intricate workings of malicious code.
- Learn how to disassemble malware binaries to uncover their hidden functionality and methods of operation.
- Master the art of debugging malware, allowing you to trace its execution flow and identify critical vulnerabilities.
- Gain proficiency in using advanced reverse engineering tools and techniques to analyze complex malware samples.
Enhance Your Malware Analysis Skills
Beyond reverse engineering, this guide delves into the realm of malware analysis, providing you with a comprehensive understanding of the techniques used to identify, classify, and mitigate malware threats.
- Discover the different types of malware analysis techniques, including static and dynamic analysis, and their applications.
- Learn how to use sandboxes to safely analyze malware without compromising your system.
- Master the art of malware reporting, enabling you to effectively communicate your findings to stakeholders.
Implement Effective Mitigation Strategies
The 'Hands-On Guide to Dissecting Malicious Software' goes beyond mere analysis, providing you with practical guidance on how to mitigate malware threats and protect your systems.
- Understand the importance of keeping your software and operating systems up to date with security patches.
- Learn how to implement effective antivirus and anti-malware solutions to protect your devices.
- Gain insights into network security measures that can prevent malware from infiltrating your network.
Become a Master of Malware Dissection
With the 'Hands-On Guide to Dissecting Malicious Software,' you will embark on a transformative journey, mastering the art of malware dissection, analysis, and mitigation.
This comprehensive guide is your indispensable companion, providing you with the knowledge, skills, and confidence to navigate the treacherous landscape of cybersecurity and protect your digital world from malicious threats.
Free Download your copy today and unlock the secrets to dissecting malicious software.
About the Author
John Doe is a renowned cybersecurity expert with over a decade of experience in malware analysis, reverse engineering, and threat intelligence. His passion for protecting digital assets drives him to share his knowledge and empower others to combat cyber threats.
Reviews
"The 'Hands-On Guide to Dissecting Malicious Software' is an invaluable resource for anyone seeking to understand and mitigate malware threats. Its comprehensive coverage of reverse engineering, analysis, and mitigation techniques makes it an indispensable guide for cybersecurity professionals and enthusiasts alike." - Dr. Jane Smith, Professor of Cybersecurity, University of California, Berkeley
"John Doe has crafted a masterpiece with the 'Hands-On Guide to Dissecting Malicious Software.' This guide is an essential addition to the libraries of security analysts, incident responders, and anyone who wants to stay ahead of the evolving threat landscape." - Mike Jones, Chief Information Security Officer, Fortune 500 Company
Free Download Your Copy Today
Secure your copy of the 'Hands-On Guide to Dissecting Malicious Software' now and embark on your journey to becoming a master of malware dissection.
Available in both print and digital formats, this guide is your ultimate companion in the fight against cyber threats.
Don't wait another day, Free Download your copy today and empower yourself with the knowledge and skills to protect your digital world.
Contact Information
For any inquiries, please contact:
John Doe
Email: [email protected]
Website: https://johndoe.com
4.8 out of 5
| Language | : | English |
| File size | : | 11518 KB |
| Text-to-Speech | : | Enabled |
| Screen Reader | : | Supported |
| Print length | : | 802 pages |
Do you want to contribute by writing guest posts on this blog?
Please contact us and send us a resume of previous articles that you have written.
 Book
Book Novel
Novel Page
Page Chapter
Chapter Text
Text Story
Story Genre
Genre Reader
Reader Library
Library Paperback
Paperback E-book
E-book Magazine
Magazine Newspaper
Newspaper Paragraph
Paragraph Sentence
Sentence Bookmark
Bookmark Shelf
Shelf Glossary
Glossary Bibliography
Bibliography Foreword
Foreword Preface
Preface Synopsis
Synopsis Annotation
Annotation Footnote
Footnote Manuscript
Manuscript Scroll
Scroll Codex
Codex Tome
Tome Bestseller
Bestseller Classics
Classics Library card
Library card Narrative
Narrative Biography
Biography Autobiography
Autobiography Memoir
Memoir Reference
Reference Encyclopedia
Encyclopedia Rey Chow
Rey Chow Lisa Mondello
Lisa Mondello Mari Carr
Mari Carr Mandee Heller Adler
Mandee Heller Adler Manik Joshi
Manik Joshi Mariano Orzola
Mariano Orzola Laura Apol
Laura Apol Salvatore Bonfiglio
Salvatore Bonfiglio Les Adams
Les Adams Philip G Joyce
Philip G Joyce Patricia Albere
Patricia Albere Letitia L Moffitt
Letitia L Moffitt Ellie Masters
Ellie Masters Linda Collins
Linda Collins Paul Taylor
Paul Taylor William Kerrigan
William Kerrigan Sarah Nooter
Sarah Nooter Liezel Graham
Liezel Graham Madeline Hunter
Madeline Hunter Marjorie Frank
Marjorie Frank
Light bulbAdvertise smarter! Our strategic ad space ensures maximum exposure. Reserve your spot today!
 Ken SimmonsImmerse Yourself in the Enthralling Realm of Cultivation with "LitRPG Random...
Ken SimmonsImmerse Yourself in the Enthralling Realm of Cultivation with "LitRPG Random...
 Terence NelsonLearn to Grow, Make, Bake, or Sew On Really Small Budget: A Comprehensive...
Terence NelsonLearn to Grow, Make, Bake, or Sew On Really Small Budget: A Comprehensive... Gil TurnerFollow ·4.1k
Gil TurnerFollow ·4.1k Ernest ClineFollow ·4.3k
Ernest ClineFollow ·4.3k Everett BellFollow ·11.8k
Everett BellFollow ·11.8k Ibrahim BlairFollow ·18.3k
Ibrahim BlairFollow ·18.3k Christian CarterFollow ·8.4k
Christian CarterFollow ·8.4k Seth HayesFollow ·3.7k
Seth HayesFollow ·3.7k Neil GaimanFollow ·16.9k
Neil GaimanFollow ·16.9k Charles DickensFollow ·3.1k
Charles DickensFollow ·3.1k

 W.H. Auden
W.H. AudenTerrorist Events Worldwide 2024: A Comprehensive Guide to...
Terrorism is a global threat that affects...
 Carson Blair
Carson BlairBeautifully Uplifting And Enchanting Novel Set In The...
Set in the beautiful West Country, this...
 Jeffrey Cox
Jeffrey CoxAn Utterly Captivating and Uplifting Story of One Woman's...
Immerse yourself in an extraordinary...

 Greg Foster
Greg FosterEngaging the Issues Through the Politics of Compassion
: The Power of...
4.8 out of 5
| Language | : | English |
| File size | : | 11518 KB |
| Text-to-Speech | : | Enabled |
| Screen Reader | : | Supported |
| Print length | : | 802 pages |